Chances are you have seen ads pop up on your screen while surfing on the internet. These pop-ups can be very annoying, especially when you are up to something important on the net. Not to mention, they slow down your productivity.
Pop-ups that occupy only a small part of your screen and don’t cover the content are reasonable. However, this is never the case at all. Some pop-ups usually take up a large portion of your screen and end up covering the content.
It gets worse when you realize the information contained in that ad is nothing remotely similar to your interests. In this guide, we will talk about the pop-up ads, types of pop up ads, and how to get rid of them so that you can enjoy the internet experience.
Table of Content
In a Rush? Here are 3 Quick and Easy Steps to Remove Popups:
- Click here to download and install Malwarebytes for your device.
- Run a full system scan by clicking the ‘Scan Now’ This process takes a few minutes.
- After the scan is complete, click ‘Remove Selected’ to remove detected threats from your device. Sometimes a restart may be required to clean your device entirely.
Alternatively, you can download Malwarebytes AdwCleaner and repeat the above steps. Malwarebytes AdwCleaner is a lightweight version specifically designed to remove adware only.
What is a Pop-up Ad?

As much as some of the pop-ups are enticing or contain information you might be interested in, they can be a bother. This happens especially when they flood your display interface, and you can’t scroll or navigate through the web page. Clicking the ‘ X ‘ option on each of these ads to close them is a short term remedy but can be tedious.
Since closing the pop-up window is a typical response, some developers behind the pop-ups usually come up with a control or button that resembles the ‘close’ or ‘cancel’ option. Clicking on these controls results in different outcomes. The outcome could be a redirect to a new pop-up or a file download that could be malicious to your system.
Types of pop-up ads
- Multi Pop-ups: These pop-up ads are generated when you open a website and are launched in multiples instances.
- Come and Go Pop-ups: These usually appear when you enter or exit a website
- Timed Pop-ups: Timed pop-ups are those designed to appear after a specific time interval.
- Mouse-over Pop-ups: As the name suggests, these appear when you move the cursor over an image or text. They are triggered by the movement of the mouse cursor and don’t need clicking.
- Floating Pop-ups: Floating pop-ups are those that, once launched over your display interface doesn’t disappear until a specified action is taken.
- Channel Opener: Commonly associated with Internet Explorer, these open a full-screen window. Firefox users are not affected by these ads.
- Modeless Window: These usually appear on the upper part of your browser and don’t disappear until the page is closed.
- Full-Screen Trap: As the name suggests, these ads launch a full screen and don’t come with a ‘close’ or ‘cancel’ option. To get rid of them, press Alt and F4 when they appear.
- Drop Down Pop-Ups: These will appear on your screen and drop down like curtains.
- Floating Banner: Found in some sites, these appear as banners flying across your screen
- Sticky Pop-ups: They appear as floating pop-ups just near one end of the screen and remain no matter how high up or low down you scroll on the page.
How to know if your device has pop-up ads?
Knowing whether your system or browser has pop up ads is simple enough. Here are the signs that will ascertain if your system has pop-up ads
- It’s a no brainer; you will see pop up ads
- You are getting bombarded with irrelevant pop-up ads.
- There are more redirects than usual.
- The browser has new toolbars and other add-ons you did not install.
- Browser tabs and windows open unexpectedly.
- The browser’s homepage has changed without your permission.
- The browser is extremely slow and sometimes crashes.
- Your device is also slow, and it shows your browser is taking all the resources.
- You get frustrated and annoyed anytime you see pop-ups while browsing.
If you experience these signs or a combination, then chances are your browser or system is flooded with pop-up ads.
How to Remove Pop-ups from your device
They’re a bunch of ways to deal with irritating pop-up ads. They include:
- Using Adblockers
Adblockers are an easy way to get rid of pop-ups. They work by blocking scripts that websites use to display ads, pop-ups, and even the ones used to open up a new tab/window when you click on a website. Some websites might break when aggressive adblockers are in use.
- Uninstalling software associated with pop-up ads
You can also deal with pop-ups by uninstalling and deleting the applications associated with pop-up ads. This way, you won’t be bothered by software that sends pop-ups upon launching or in the background when you are not using them. This comes at a cost especially if it’s a software you have to use often.
To avoid being left ‘stranded,’ you can find an alternative software that helps you accomplish the same task as the uninstalled software.
You can also uninstall odd software from your system. If you start noticing pop-up ads on your screen recently that were not there before, consider uninstalling the latest software that you added.
- Using the Control Panel of a pop-up blocker
Some pop-up blockers come with a control panel that you can use to prevent control how pop-ups appear. To do this, visit the privacy tab in the control panel under the ‘internet options’ and turn on the toggle switch on pop –up blocker and set the level of filter that suits you. Note that this blocking will prevent all pop-ups from appearing on your screen which means you might miss the ads that you like or are interested in.
- Adware software
An adware software such as Malwarebytes AdwCleaner is the best solution for dealing with malware induced pop-ups. You can also use Malwarebytes. This software gets rid of malware, prevents further malware infection, and protects your device against all sorts of malware. To get rid of malware induced pop-ups using Malwarebytes AdwCleaner proceed as follows.
- Download and install Malwarebytes AdwCleaner.
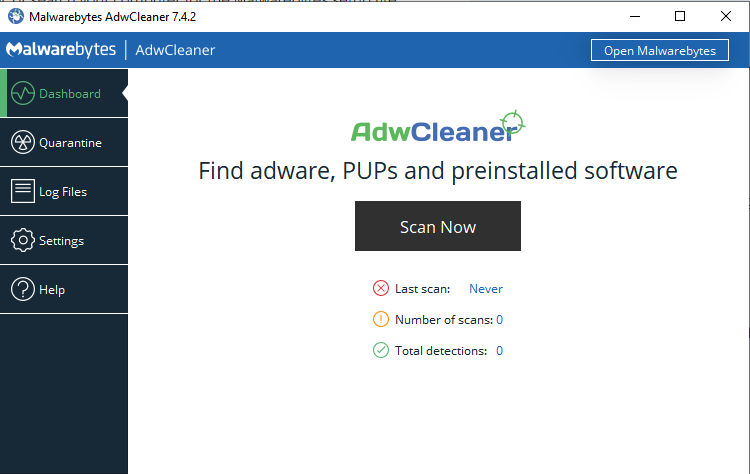
- Launch the tool and on the Dashboard section, click the Scan now button and wait for a few minutes.
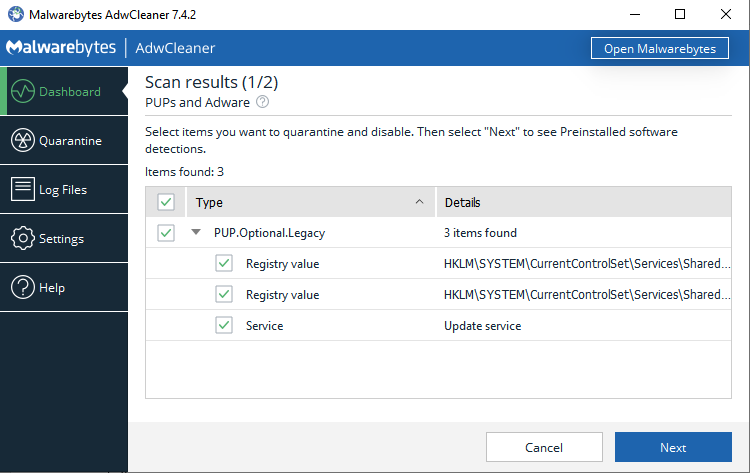
- On the results that show up, select the items you want to quarantine/disable, if any.
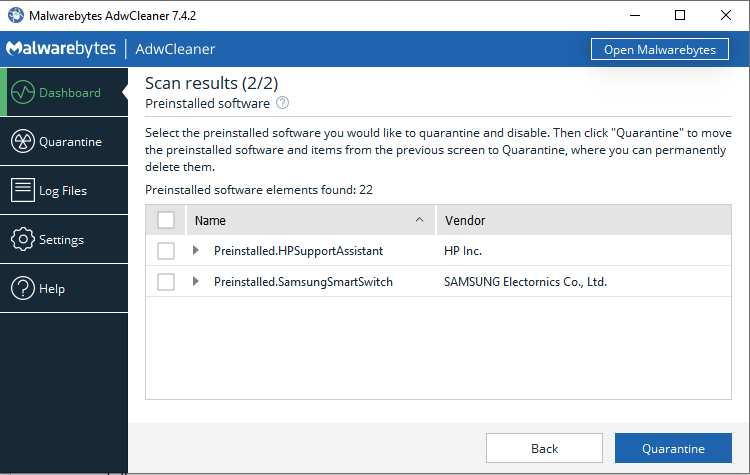
- Click the next button to select preinstalled software you want to quarantine/disable – the detected software might be the one injecting pop-ups.
- Lastly, click the Quarantine button to move selected items to the quarantine section.
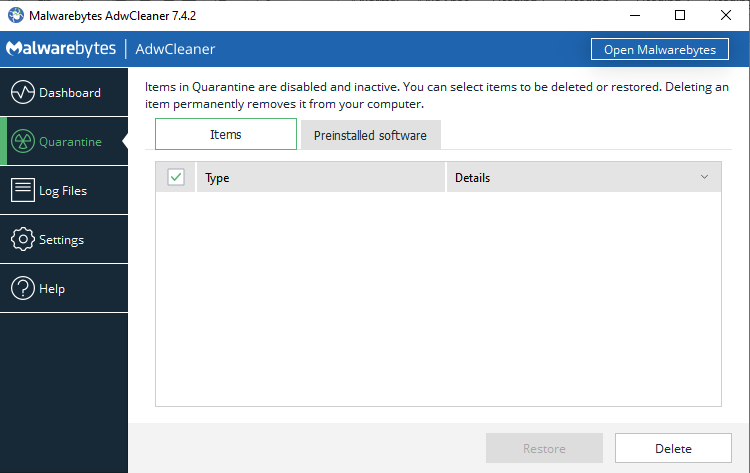
- If you want to get rid of the detected items, open the Quarantine section, and click the Delete
Best pop-up removal tools
The following antimalware/antivirus solutions may help in dealing with pop-ups, especially those caused by malware infections.
- Bitdefender
Platform: Windows, Mac, iOS, Android

You can subscribe to the package that meets your needs. The premium subscription packs a 30-day free trial period. The installation process is easy after downloading the software. Bitdefender has a systematized interface as well as user-definable functionalities.
To scan your device, click the scan button. Bitdefender will let you know if your device is clean through a green check on the dashboard. The autopilot function helps choose an operation mode for your device regarding the task you are doing.
Download Bitdefender and get rid of pop-up ads in a quick scan.
- Kaspersky
Platform: Windows, Mac, iOS, Android
Kaspersky is a world-class leader antivirus that is known for its efficiency and higher detection rate. All Kaspersky products have been vetted through various tests, and the results are amazing. Although Kaspersky has had some downs especially with the spying allegations, its antivirus products are still unmatched. Kaspersky uses machine learning and a behavioral model antivirus engine that is capable of even detecting zero-day threats and infections. Although it does not sport many features like other antivirus products, Kaspersky’s core features and functionality are enough to protect your devices from malware.
Kaspersky antivirus products protect your devices in four modules. They include; File protection, email protection, web protection, and real-time protection. With these modules, Kaspersky is capable of detecting, deleting and preventing infections from various types of malware such as Trojans, worms, and viruses. Kaspersky also offers other additional features for various functionalities such as encryption, browser and webcam protection, a backup system, a password manager, a firewall, a VPN, and even a game mode. Using Kaspersky is also a straight forward right from installation. Its interface features fluid navigation for easy access to features. Although it scans take a while, your device’s performance is not affected, and the result will be a thoroughly cleaned device. Kaspersky products come with a 30-day free trial.
Download Kaspersky and get rid of pop-up ads in a quick scan.
How to avoid pop-up ads in the future
- Implement useful preventive measures like avoiding visiting the websites that are flooded with ads
- Avoiding clicking on suspicious links and URLs especially those from torrent sites
- Do not install and use applications from unknown sources or sources that are not credible. Also, avoid software that comes with pop-ups bundled in them.
- Always use your browser’s adblocker or pop- adblocker tool.
- Ensure your antivirus software is always running in the background to block any pop-up ads that may be generated elsewhere in the system
FAQS
What is a Pop-up Window?
A pop-up window is a window that opens on top of the main browser window, which usually has advertising content such as text or images.
What are Pop-up Blockers?
These are tools that integrate into the system or browser to prevent ads from appearing. They help give you a smooth Internet experience.
I turned on the pop-up blocker, but I still see some pop-ups. Why?
Some software may open up windows without your permission. To solve this issue, you have to know the specific software that is causing the pop-ups and then deleting it or altering its settings to prevent the ads from appearing.
Can I choose to allow pop-ups from a specific website in a browser?
Yes, if you want some websites to show ads, you can set your browser’s settings to allow that particular site to send ads. Check your ad blocker and whitelist those sites so that the adblocker lets you receive ads from those sites.
Can I set the browser to block all pop-ups?
Just like you can make an exception, you can also block all ads regardless of the site they are from. Check the browser’s settings and also the browser’s adblocker or blocking tool that is integrated into the system. Make sure to select and toggle on the option that lets all the ads be blocked.
Wrap up
Most pop-ups are indeed annoying and can also threaten your privacy and security on the internet. To ensure you are safe, use the ways and measures mentioned above.